Uncompromising data security for right-time data
Estuary unifies real-time and batch data movement onto a single stream processing platform, delivering data pipeline security for the most demanding enterprise workloads.
Flexible deployment, unwavering security: tailored for every enterprise
Estuary’s Zero-Trust architecture supports any enterprise deployment model: managed VPC, private network, or hybrid cloud. We fit your environment and keep your data secure wherever it resides.
Enterprise-grade trust & compliance: built on verified standards
At Estuary, safeguarding customer data is a core priority. We undergo independent audits and align with leading global security and privacy standards. As a SOC 2 data platform, Estuary supports enterprise security reviews, procurement requirements, and regulated workloads.
Our commitment to operational excellence
Certifications are only the starting point. Security is woven into everything we do, from continuous monitoring and mature incident-response workflows to regular team-wide security training. The result: uncompromising data protection and a resilient platform you can trust.
Contact UsHolistic security architecture: Protecting your data in motion
Data Protection
Encryption & Integrity - Every byte secured in motion and at rest.
Identity & Access
Authentication & Isolation - Strict, role-based controls for every connection.
Network Security
Connectivity & Compliance, Private pathways shield data from public exposure.
Operational Security
Monitoring & Auditing - Continuous oversight ensures transparency and trust.
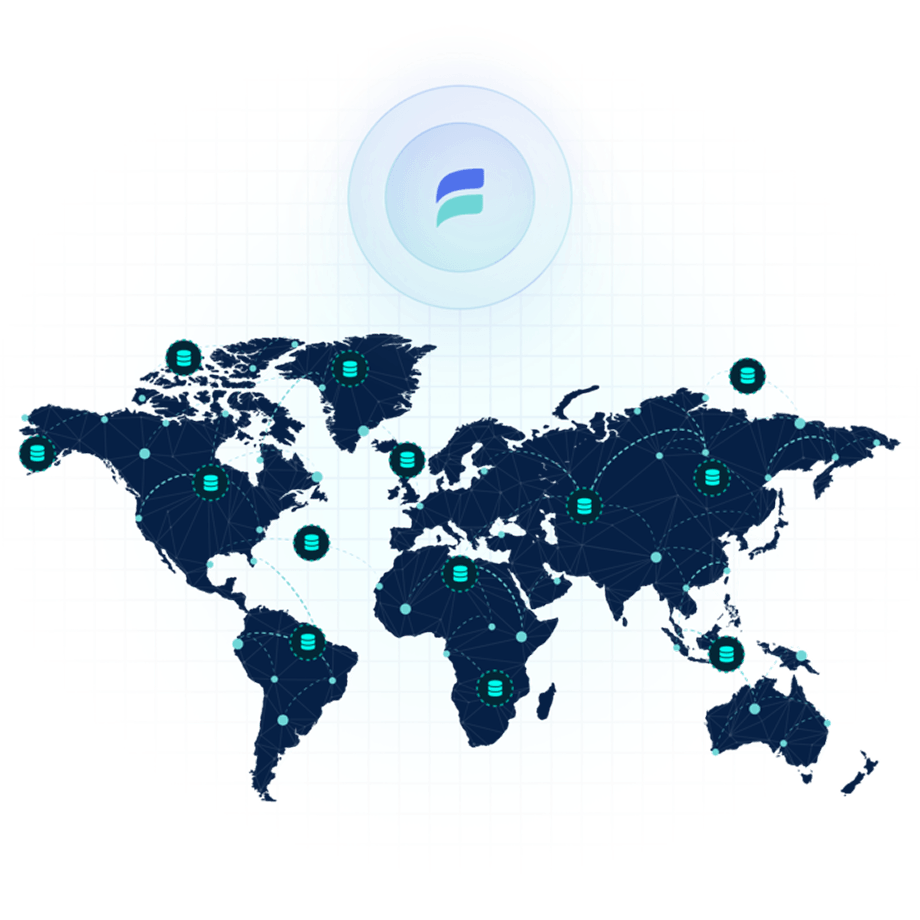
Global reach, unified security
Deploy Estuary data planes across multiple regions to meet compliance requirements, optimize latency, and strengthen disaster recovery. Every region operates under the same Zero-Trust framework, keeping your data encrypted, compliant, and resilient: wherever it lives.
Public data planes
US Central (Iowa)
Google Cloud Platform
US East (N. Virginia)
Amazon Web Services
US West (Oregon)
Amazon Web Services
Europe (Ireland)
Amazon Web Services
Asia Pacific (Sydney)
Amazon Web Services
Private data planes
Your environment, any region
Run private data planes on Amazon Web Services, Google Cloud Platform, and Microsoft Azure, or on-premises within your networks.
Choose regions across those clouds or your own sites to meet compliance, residency, and latency requirements.
Secure connections, private by design
Trust begins with how your data connects. Estuary offers fully encrypted pathways across cloud, on-premises, and hybrid environments: linking your systems without ever exposing your network.
Secure Connectivity Across Any Environment
Estuary connects seamlessly across AWS, Google Cloud, Azure, and on-prem servers. All connections use RSA private key authentication aligned with IAM policies, and optional IP allowlisting ensures secure setup without sacrificing control.
Reverse SSH Bastion
For Private or BYOC deployments, Estuary provides a managed bastion host for secure internal access. Reverse SSH tunnels eliminate firewall changes while maintaining full encryption and visibility.
SSH Tunneling
Safely connect to internal databases and services without exposing them to the public internet. Estuary supports encrypted SSH port forwarding, keeping every data stream secure from source to destination.
PrivateLink Integration
Private or BYOC deployments can connect through AWS PrivateLink, GCP Private Service Connect, or Azure equivalents. This ensures data stays fully private, never leaving your controlled network or touching the public internet.
Trusted by industry leaders
Teams rely on Estuary to move data securely and consistently across modern data stacks.
Security and compliance FAQs
Transparency you can trust.
Where is my data stored and processed?
Data is stored in your own cloud account, not in Estuary’s. Whether you’re using SaaS or a Private Deployment, your data flows through infrastructure you control, within regions you select. The platform supports zero data egress from your network.
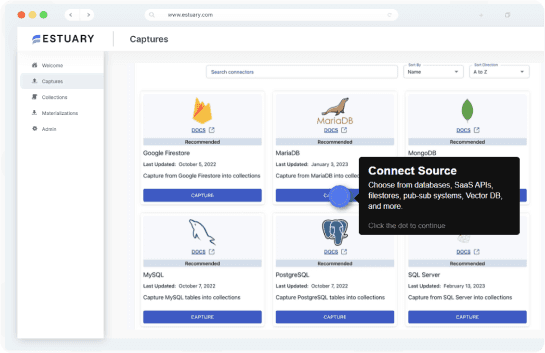
What are Private Deployments in Estuary?
Private Deployments let you run the data plane inside your own VPC or cloud region, while the SaaS control plane manages configuration. Your data never leaves your network, and you retain full control over infrastructure, security, and governance.
Does Estuary support private networking and secure access?
Yes. Estuary supports AWS PrivateLink, VPC peering, and SSH tunnels, enabling secure connections to firewalled databases and private cloud services. You can deploy the data plane in any region while maintaining full network isolation.
How does Estuary encrypt data in transit and at rest?
All communications use TLS, including within cloud environments. Internal services authenticate with mutual TLS (mTLS) using a custom certificate authority per deployment. Server-facing services use Let’s Encrypt, and all data at rest is encrypted with AES-256.
Can I restrict or audit data access across deployments?
Yes. Estuary uses RBAC (Role-Based Access Control) and tokenized cross-deployment access. The control plane handles authorization and generates traceable, time-limited tokens, ensuring secure access and full auditability across data planes.
Does Estuary provide centralized logging and monitoring?
Yes. Platform-level logs are shipped from each data plane to a centralized logging system, and task-level logs are accessible via the Flow interface. This enables both internal security monitoring and user visibility.
Can I move data planes across regions without compromising security?
Yes. Estuary’s architecture supports multi-region data plane mobility without relying on specific VPC constructs. You can maintain consistent security policies across geographies while ensuring data residency compliance.